Fully Web-Based Secure-By-Design UCaaS Platform
What Does It Really Mean?

Secure by design means a complete overhaul of conventional security.
With collaboration and business as a whole now primarily taking place online, cybersecurity is paramount to businesses. But too many businesses rely on vulnerable “secured” systems that require extensive upkeep and compatibility checks rather than opting for secure-by-design options. So what’s the difference? Is the distinction insignificant, or is one truly more secure than the other?
The reality is that while a secure system can in theory be protected from malicious actors, vendors often fail to ensure all parts of their comms are secure, leading to critical vulnerabilities. Here’s what ends up happening.

SECURED SYSTEMS
This is the framework for many secured systems:
From this, we can see that the system has security added on, in the form of a firewall. In this case, the security is only as good as the configuration of the firewall.
Let’s make the system a little more complex by adding in a DMZ, an area that the public can access without accessing the main WAN.
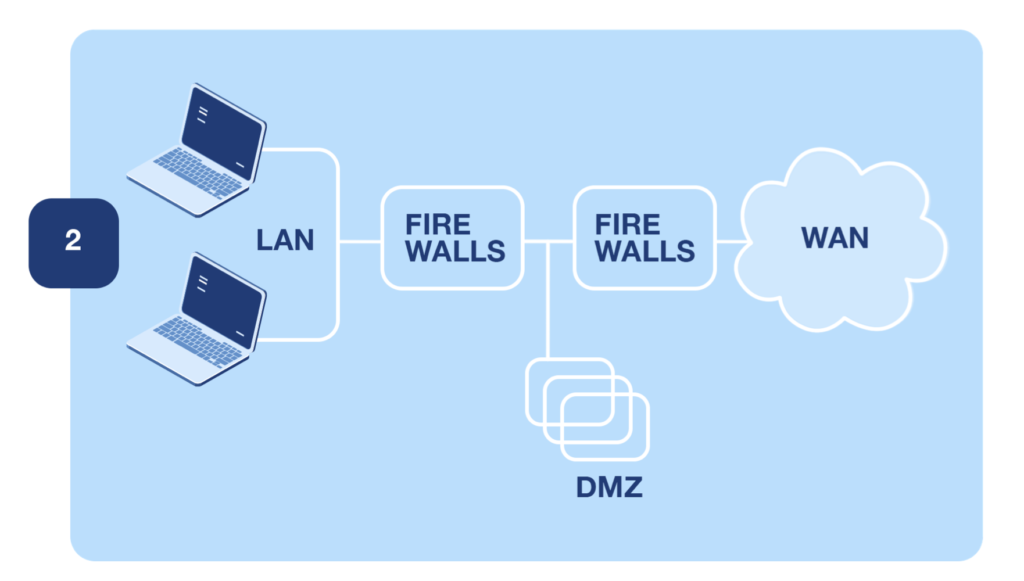
In this case, the two firewalls have to be configured perfectly to allow traffic through. And if you follow the industry standard of having firewalls from different providers, it doubles the chance for a misconfiguration to occur, making access difficult for legitimate users.
In both of these cases, the firewalls are added on top of existing architecture, an example of a secured system. You might also add in an SBC, which allows VoIP traffic through. Again, this must be configured to act in harmony with the two firewalls and the rest of the systems.
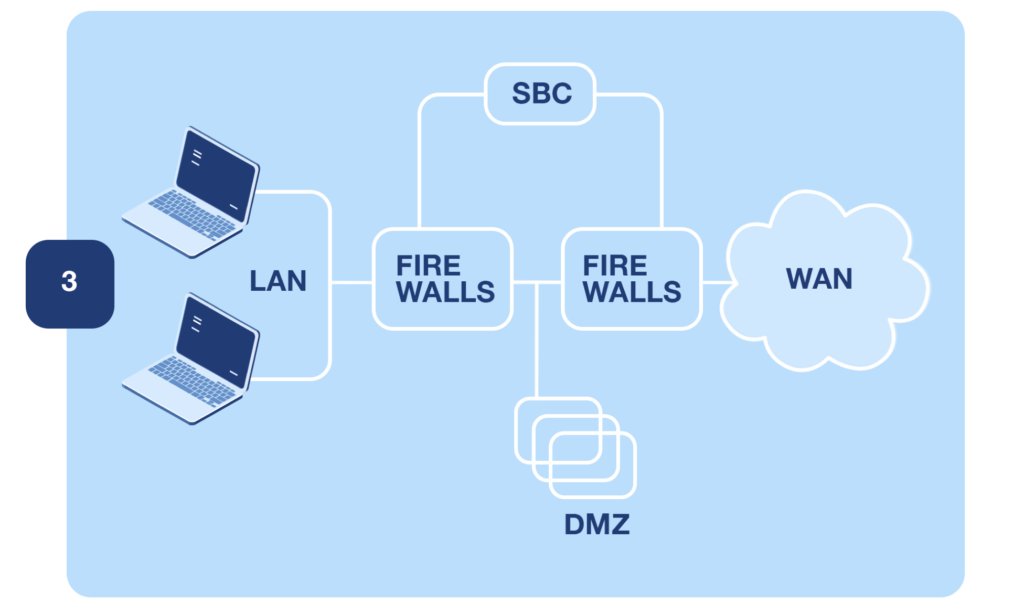
Each point represents a critical junction, a point of failure. And it’s these points of failure that allow people in who aren’t supposed to be there.
Our Solutions are Secure by Design, Offering a Better Route to Cybersecurity
Talk to our expert and book a demo today
System Monitoring
Even the most secure system requires some form of monitoring, and good secure-by-design principles accept there’s always a risk of intrusion. This means things like:
- Automatic alerts across all devices managed by the PBX
- Alerts for attacks originating from within the system
- Integrations with common monitoring software
- Behavioral-based alerts where possible
When you’re a local MSP, you must ensure your data is protected and that the systems you install are appropriately monitored. Secure by-design systems either integrate or make it simple to add monitoring tools without fuss.
In this particular instance, secure-by-design systems don’t have to be that different from secured systems, although many secured systems do not automatically include monitoring capabilities or automation.
Secure by design solutions are much more effective than secured systems as they come with much of the security you need already baked in. And if you choose the complete Wildix ecosystem, you get all that security baked in.
Ready To Reach New Heights? Let's Get There, Together.

READY TO TALK TO SALES?
CONTACT US:
905-123-1234 |. EMAIL US
Connect with us
Request a call back
Send us a message and we’ll get back to you as soon as possible!
